DevOps Articles
Curated articles, resources, tips and trends from the DevOps World.
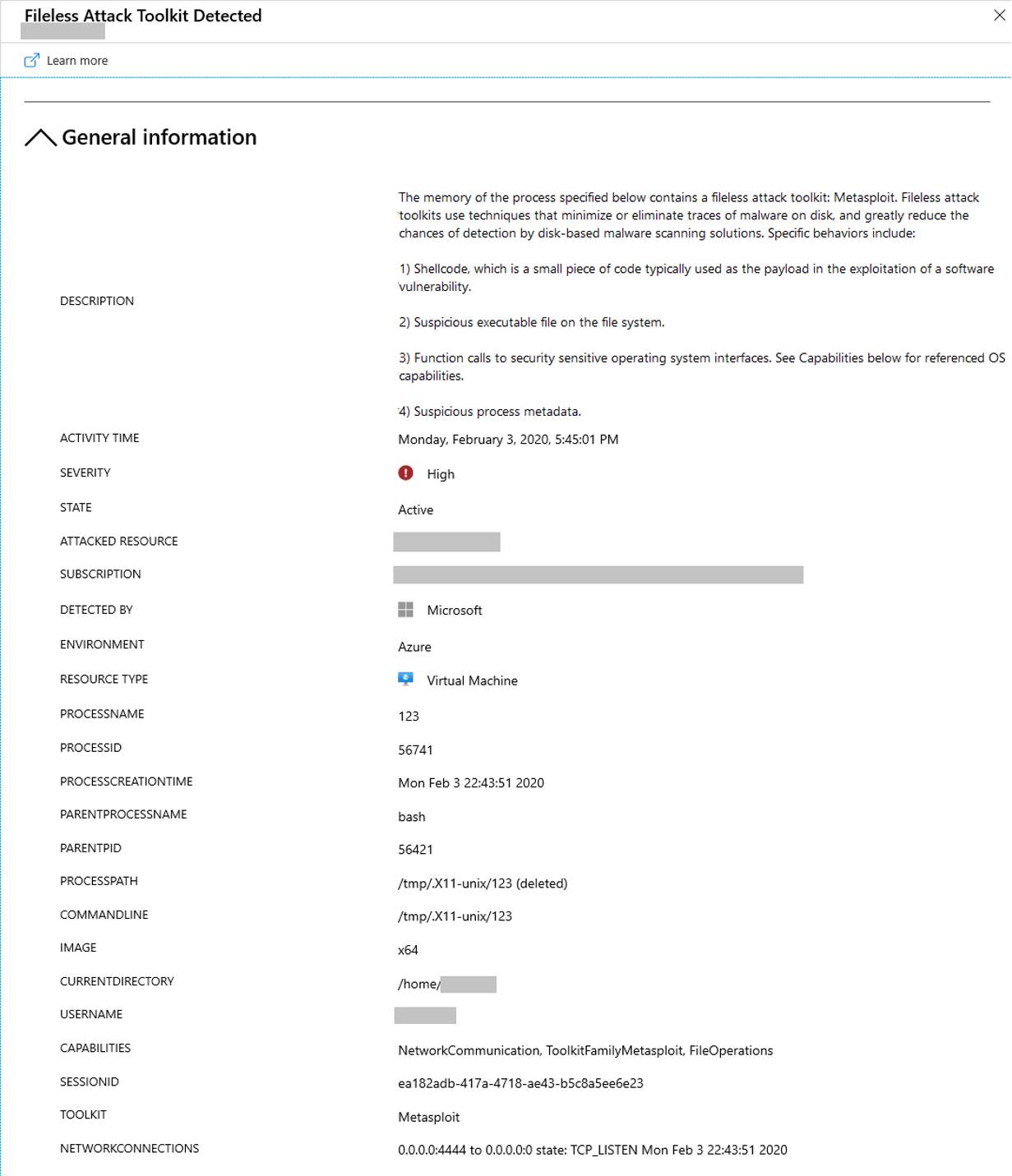
Fileless attack detection for Linux in preview
6 years ago
azure.microsoft.com
Summary: This is a summary of an article originally published by the source. Read the full original article here →
This blog post was co-authored by Aditya Joshi, Senior Software Engineer, Enterprise Protection and Detection. Attackers are increasingly employing stealthier methods to avoid detection.
Product
Useful Links
Made with pure grit © 2026 Jetpack Labs Inc. All rights reserved. www.jetpacklabs.com